- Websites often use GTM scripts to collect and record information about their visitors.
- Before the patch, the hacker made four transactions totaling $265,000 worth of tokens.
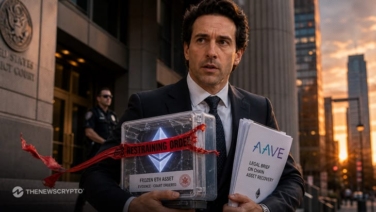
The KyberSwap decentralized exchange (DEX) has become the latest DeFi initiative to be attacked, after last month’s Curve Finance vulnerability. The liquidity protocol upon which KyberSwap is based, the Kyber Network, acknowledged claims on Friday and said the assault on its website had been spotted and repaired within a few hours.
1/ ❗️Notice of Exploit of KyberSwap Frontend:
— Kyber Network (@KyberNetwork) September 1, 2022
We identified and neutralized an exploit on the KyberSwap frontend. Affected users will be compensated. We have summarized the details in this thread⬇️
According to the company’s statement, the criminals gained access to the app’s front end by exploiting a vulnerability in the Google Tag Manager (GTM) script.
Patch Too Late
Websites often use GTM scripts to collect and record information about their visitors. Hackers forced consumers to accept their payments before sending them to the hacker’s address using the malicious script injected through GTM. Before the patch, the hacker made four transactions totaling $265,000 worth of Aave Matic USDC (AMUSDC) tokens.
So far, Aave has been implemented on Ethereum and various other blockchains, including Polygon. The aforementioned token is an Aave Polygon-integrated USDC stablecoin. Users get the interest-bearing token whenever a token of this kind is placed on the lending platform. The version that was stolen by hackers on Friday was the one that accrued interest.
Kyber Network recommended that all users verify their approvals using the polygonscan approval feature by the block explorer. Kyber Network has promised the hackers a $40,000 reward—15 percent of what they stole—if they can return the money. The remainder of the payment is to be sent to the company’s designated wallet address.
The crypto sector has been hacked again and again. Hackers find unique ways to exploit platforms and often don’t return the stolen funds despite the bounty.
Recommended For You: